
PDF) Short paper: Exploiting WPA2-enterprise vendor implementation weaknesses through challenge response oracles
really confused about PEAP and MS-CHAP v2. Why sometimes they are separated and sometimes one is the option of the other one? : r/sysadmin

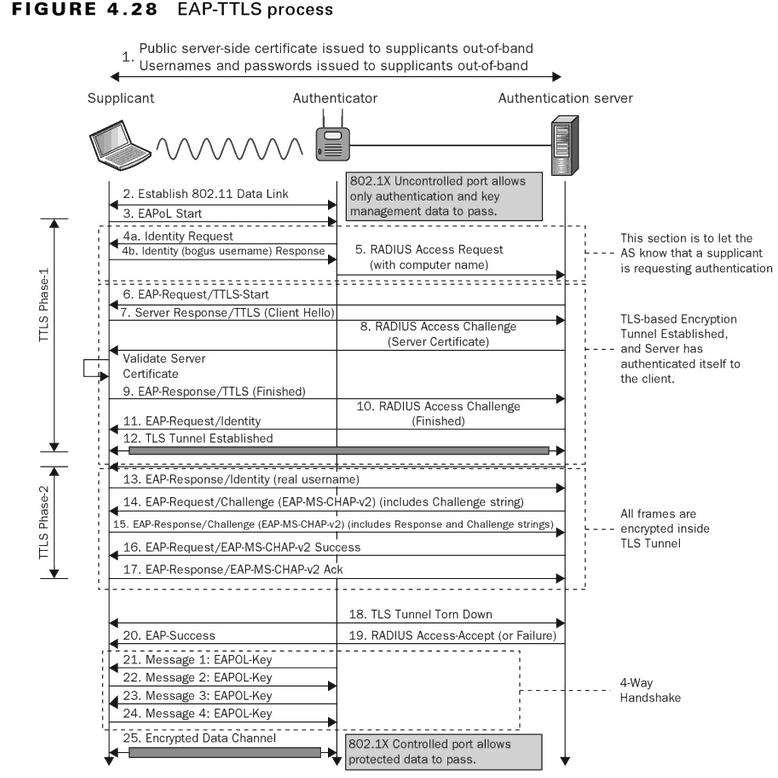
Table 1 from Network access authentication infrastructure using EAP-TTLS on diameter EAP application | Semantic Scholar

![MS-PEAP]: Overview | Microsoft Learn MS-PEAP]: Overview | Microsoft Learn](https://learn.microsoft.com/en-us/openspecs/windows_protocols/ms-peap/ms-peap_files/image001.png)


![MS-CHAP]: Overview | Microsoft Learn MS-CHAP]: Overview | Microsoft Learn](https://learn.microsoft.com/en-us/openspecs/windows_protocols/ms-chap/ms-chap_files/image001.png)




![PDF] A Threat Analysis of The Extensible Authentication Protocol | Semantic Scholar PDF] A Threat Analysis of The Extensible Authentication Protocol | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/c01862ea3f9cc0b9ed081ce67831410f14c5d62d/25-Table6-1.png)